It would seem that decentralization and anonymity go hand in hand. But they don’t! Some people will probably be surprised, but many transactions can be tracked on the blockchain. Even the most heavily encrypted cryptocurrencies, such as Monero, DASH, and Verge, can be tracked to a certain extent. This is due to the very nature of blockchain. Every transaction is recorded and stored in a ledger available to all.
Surprised? Probably, that’s the reason some people in crypto are so paranoid.
To start with, it is worth separating two essential concepts. Anonymity means that the name of the actor is unknown. But his actions are known. And confidentiality is the ability of a person or group to isolate themselves or information about themselves. To make it even simpler, anonymity is hiding the “who,” and privacy is hiding the “what.”
Big Brother is watching. Always
In the blockchain, anonymity means that parties can exchange data without revealing anything about their identity offline. For example, each Bitcoin owner’s address is a public key hash; it is not private because you can see all transactions made from and to that address.
The brand new newsletter with insights, market analysis and daily opportunities.
Let’s grow together!
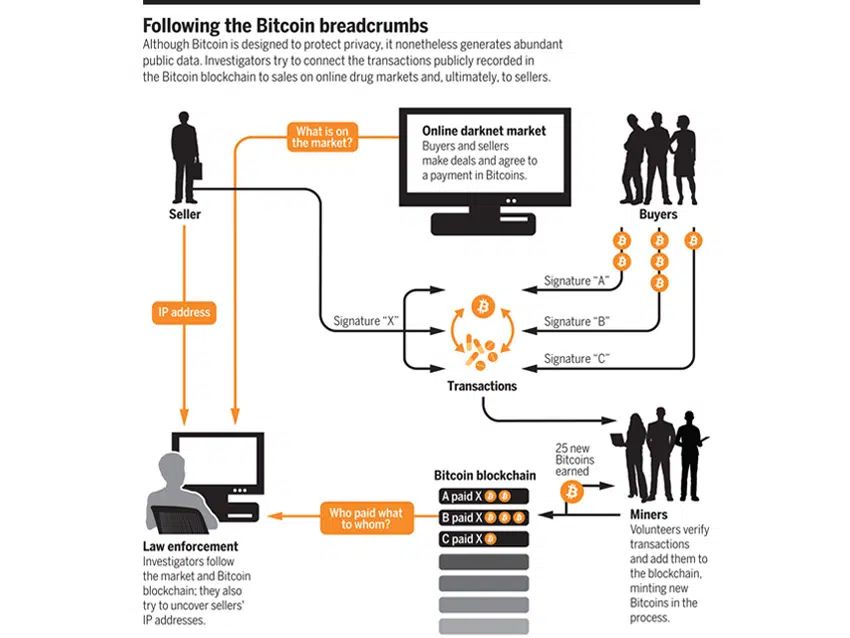
When a BTC transaction takes place, all of its data, including its source address, is permanently stored in a public registry. And anyone can see the balance and transaction history of any Bitcoin address. This data remains anonymous as long as the address is not associated with a physical identity.
However, this can be difficult to achieve. The connection can appear when you register with an exchange that implements KYC or Know Your Customer procedures (all financial institutions, including cryptocurrency exchanges, are required to identify and verify the identity of each client). Or when you post an address on a personal blog to get donations.
You can generate a new address and use it for an anonymous transaction. But in fact, if someone really wants it, the identity of the owner of the address can be established. To create a new address for a transaction, you must first top up the address from which you want to make the payment. In the end, that’s how you can trace the information you wish to. All you need is the desire and time.
Bitcoin is a regular P2P (peer-to-peer is a decentralized communications model in which each party has the same capabilities and either party can initiate a communication session), so users can be attacked even at the network level. Anyone between the user and the Bitcoin network (such as an Internet Service Provider) can easily reveal the IP address. Also, authorities can demand access to this information.
Shopping buffs, this is for you
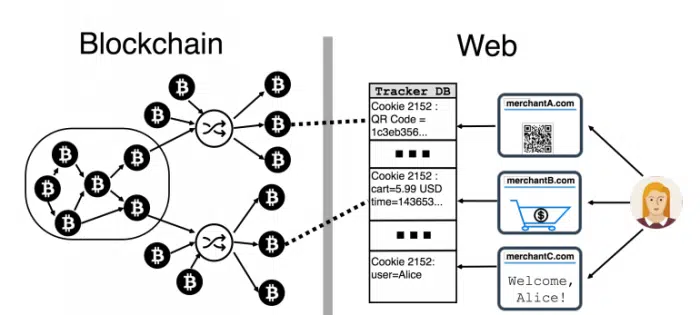
According to MIT Technology Review, leaked information during purchases makes it easy to link people to their Bitcoin transactions, even when shoppers use additional privacy protections such as CoinJoin.
The danger is posed by web trackers and cookies — small pieces of code embedded in websites that send third parties information about how a user uses the site. Common web trackers send data to Google, Facebook, and other companies to track page usage statistics, the amount spent on purchases, browsing habits and interests, and so on. Some trackers even send companies personal information such as name, address, and email. And once the information about the transaction gets on the Internet, intruders can easily obtain it. And use it against you.
“If the victim employs 3 rounds of CoinJoin and the adversary observes two of the victim’s payments, he can link them back to her wallet (despite mixing) with 98% accuracy,” Steven Goldfeder at Princeton University says.
How to hide your ass
- Customers can protect themselves using tools such as Ghostery, AdBlock Plus, or uBlock Origin in their browsers.
- Use Bitcoin mixing. This process tries to break connectivity or traceability by creating temporary addresses or exchanging coins for other addresses of the same value. This makes it difficult to trace in the blockchain.
- Use the Tor browser to connect to the Bitcoin network. Tor is a committed, voluntary community that believes in anonymity and Internet use without being tracked. Tor nodes encrypt and direct your Internet traffic to random computer nodes on the Tor network before it reaches its final destination. It makes it extraordinarily difficult to determine the IP address or system from which a message or transaction was transmitted.
- Don’t forget about a logless VPN. A logless virtual private network (VPN) does not store a user’s activity history on its servers. But it encrypts all Internet traffic and routes it through multiple servers of the user’s choice in different locations before it reaches the final destination. Some logless VPNs also maintain a shared IP address for multiple users, making it challenging to identify and track a person’s identity. Here are a few popular logless VPN providers outside the USA: NordVPN and VPNArea.