After rigorous investigation, a suspect in connection to the heist of $8.5 million from the decentralized finance platform, Platypus, has been identified.
In a tweet posted on Feb 16, 2023, the blockchain security company CertiK was the first to flag a flash loan attack on the Avalanche-based stable swap platform. The tweet reveals the suspected perpetrator’s contract address.
We are seeing a #flashloan attack on @Platypusdefi resulting in a potential loss of ~$8.5M.
Tx AVAX: 0x1266a937c2ccd970e5d7929021eed3ec593a95c68a99b4920c2efa226679b430
Stay Frosty! pic.twitter.com/AM2HOM5M2r
— CertiK Alert (@CertiKAlert) February 16, 2023
The brand new newsletter with insights, market analysis and daily opportunities.
Let’s grow together!
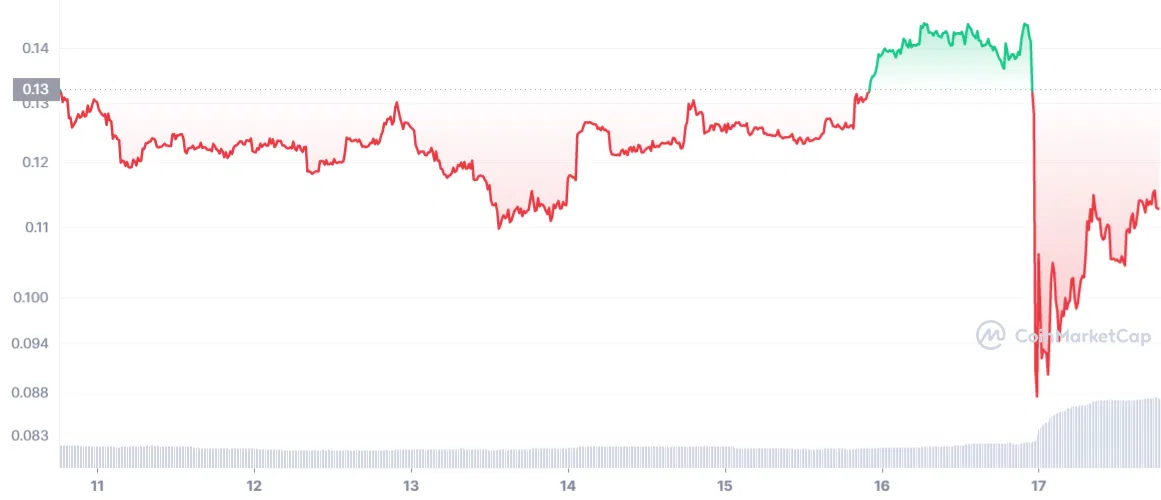
CertiK has disclosed that the $8.5 million has already been transferred, causing the Platypus USD stablecoin to become detached from the U.S. dollar. Its value plummeted by 26.72% in the last 24 hours, to $0.1046 on the morning of Feb 17, 2023.
Afterward, Platypus took to Twitter to verify the breach, while a Platypus Telegram group moderator corroborated that trading had been put on hold.
“The attacker used a flashloan to exploit a logic error in the USP solvency check mechanism in the contract holding the collateral.”
Not all was lost
Moreover, Platypus officially announced the unfortunate deficit was from its primary reserve and reassured depositors that 85% of their funds would be restored.
Furthermore, the incident only impacted the primary reserve, and other reserves remain unscathed. To retrieve the stolen funds, the company has reached out to the hacker to initiate negotiations for a reward.
In response to the heist, Tether Holdings has put a freeze on the USDT. Additionally, Platypus got in touch with Circle and Binance, urging them to suspend any other stolen tokens.
Dear Community,
We regret to inform you that our protocol was hacked recently, and the attacker took advantage of a flaw in our USP solvency check mechanism. They used a flashloan to exploit a logic error in the USP solvency check mechanism in the contract holding the collateral.— Platypus 🔺 (🦆+🦦+🦫) (@Platypusdefi) February 17, 2023
Hacker put on blast, deactivates Twitter account
Crypto investigator ZachXBT, known for his meticulous analysis of blockchain data, has brought attention to a Twitter account with the handle @retlqw, which has since been removed. ZachXBT claims that the addresses pinpointed by Platypus are associated with said account.
“I’ve traced addresses back to your account from the @Platypusdefi exploit and I am in touch with their team and exchanges. We’d like to negotiate the return of the funds before we engage with law enforcement,” said ZachXBT.
ZachXBT’s statement was amplified when Platypus’ official Twitter account retweeted the message.
Hi @retlqw since you deactivated your account after I messaged you.
I've traced addresses back to your account from the @Platypusdefi exploit and I am in touch with their team and exchanges.
We’d like to negotiate returning of the funds before we engage with law enforcement. pic.twitter.com/oJdAc9IIkD
— ZachXBT (@zachxbt) February 17, 2023
It was a flash attack
The technique used in the recent hack on Platypus, known as a flash attack, is akin to the approach employed by Avi Eisenberg.
Avi supposedly tampered with the value of the MNGO token in October 2022. He defended his actions by claiming that all his activities were lawful, above-board market maneuvers, and executed within the framework of the protocol.
However, the authorities apprehended Eisenberg on fraud allegations on Dec 28, 2022.